
Intelligent Security Tools by AWS – Amazon GuardDuty and Amazon Macie
In a world full of innovate and menacing cyber attacks like phishing, SQL Injection, Denial of Service and etc., it has become even more imperative to have innovations and intelligence in cyber security as well. It is important to safeguard the vital information, data, cyber assets and systems with the help of intelligent tools and machine learning to take the security in hand onto a next level.

Amazon Web Services facilitates the intelligent threat detection and protection tools via services like Amazon GuardDuty, responsible for continuous monitoring of the events from other security services like CloudTrail and the and Amazon Macie, responsible for identifying and protecting sensitive data. The security pillar of AWS Well Architected Framework blankets the potential to protect the aforementioned while achieving business value through risk assessments and mitigation strategies. Detailed description of how Amazon GuardDuty and Amazon Macie facilitates the intelligent threat detection and protection is given below.
AWS GuardDuty
Amazon GuardDuty is a threat detection service that persistently screens for malignant action and unapproved conduct to ensure your AWS records and workloads. With the cloud, the assortment and conglomeration of account and network activities is streamlined, yet it tends to be tedious for security groups to constantly investigate occasion log information for potential dangers. With GuardDuty, you currently have a keen, savvy and cost-effective alternative for nonstop anomaly discovery in the AWS Cloud. The administration utilizes machine learning, oddity discovery, and coordinated threat intelligence to distinguish and prioritize potential threats. GuardDuty breaks down several billions of occasions over various AWS information sources, for example, AWS CloudTrail, Amazon VPC Flow Logs, and DNS logs. With a couple of snaps in the AWS Management Console, GuardDuty can be empowered with no product or equipment to send or keep up. By incorporating with Amazon CloudWatch Events, GuardDuty cautions are noteworthy, simple to total over different records, and direct to drive into existing occasion the executives and work process frameworks.

Prominent Features of GuardDuty
- Account-Level Threat Detection – GuardDuty can accurately detect a compromise with the AWS account while continuously monitoring it in near real-time.
- Continuous Monitoring Across AWS Accounts — GuardDuty monitors and analyzes the entire AWS account and all the subsequent workloads event data found in AWS CloudTrail, VPC Flow Logs and DNS Logs without additional security software or infrastructure requirement.
- Threat Detections Developed and Optimized for the Cloud – GuardDuty has built-in detection techniques that are specifically developed and optimized for the AWS Cloud. GuardDuty also has integrated threat intelligence with industry-leading third-party security integrations possible, such as Proofpoint and CrowdStrike.
- Threat Severity Levels for Efficient Prioritization — GuardDuty features low, medium, and high priority threat severity levels so customers can respond accordingly.
- Automate Threat Response and Remediation — With GuardDuty, one can utilize HTTPS APIs, CLI tools, and AWS CloudWatch Events to support automated security responses.
- Highly Available Threat Detection — GuardDuty can automatically manage resource utilization depending on overall activity levels within the AWS accounts and workloads. GuardDuty adds detection capacity when necessary and reduces utilization when it’s no longer needed.
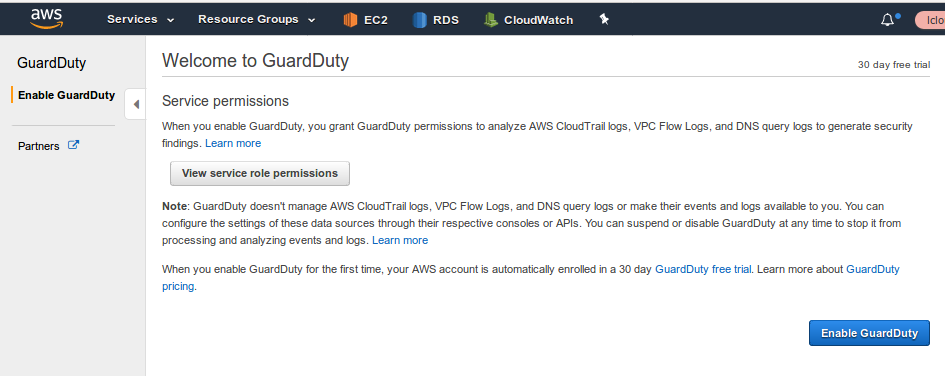
- One Click Deployment Without Additional Software or Infrastructure – GuardDuty Simplifies deployment and management with quick enabling and one click deployment without any additional infrastructure to deploy and manage.
Implementation Guidelines
Before the implementation of the of the Amazon GuardDuty, we initiated by calculating the cost of implementing the services based on the number of incoming requests to CloudTrail and the overall size of the VPCFlowLogs. The exercise was done for a customer account having approximately 42 instances. The cost calculated for the service implementation was about USD12 per month. The implementation of GuardDuty is very effortless, since the service activation is just one click away.
AWS analyses the events from various sources like CloudTrail and etc. in real time. Once these events match the present pattern, GuardDuty marks them as Findings.

Such events as mentioned above are therefore bifurcated into groups, based on the priorities. Post this, an event gets generated and is sent to CloudWatch wherein it filters them aptly. A notification is sent in a response of this AWS event.

Every event which is reported by Amazon GuardDuty consists of the details and a brief about the risk, time and date stamp, event type, instance details, etc. along with a link to the AWS documentation describing the details of the risk.

AWS Macie
Amazon Macie is one amongst the many fully managed service by AWS which enables the end user to discover, classify and secure the sensitive data. Amazon Macie uses machine learning and pattern matching algorithms in the background to bifurcate the data available in the Amazon S3 bucket to automatically spot and segregate data for the end customer.

Prominent Features of Amazon Macie
- Discover Sensitive Data at Scale – Amazon Macie uses machine learning and pattern matching algorithms to discover sensitive data at scale. It also allows the end user to define their own custom sensitive data types, hence they can discover and protect the sensitive data that may be unique to one’s business or use case.
- Visibility to Data Security Posture – Amazon Macie gives constant visibility of the data security and data privacy of the data stored in Amazon S3. Macie automatically and continually evaluates all the S3 buckets and alerts to any unencrypted buckets, publicly accessible buckets, or buckets shared with AWS accounts outside those that have been defined in the AWS Organizations.
- Easy Setup and Management – Getting started with Amazon Macie is fast and easy with one-click in the AWS Management Console or a single API call. Macie provides multi-account support using AWS Organizations; hence the Macie enablement is a few clicks away for all.
- Superior Visibility of Data — There is a clear management visibility for the security administrators into the data storage environments.
- Machine Learning Enabled Data Security Automation — Amazon Macie enables discovering, classifying, and protecting the data stored in AWS is an automated fashion. This helps in quick and better understand of the location of the sensitive information and means of its access.
- Custom alert monitoring with CloudWatch — Amazon Macie can send the reports and findings to Amazon CloudWatch Events to build custom remediation and alert management for the security ticketing systems.
Implementation Guidelines
Enabling Amazon Macie
In the Macie console, select “Enable Macie”. If you’re using AWS Organizations, you can delegate an AWS account for the complete and bifurcated administration of Macie for your Organization.

Once Macie is enabled, it automatically delivers a brief of the S3 buckets associated to the account in a region. It also evaluates these buckets in a continuous mode thereby generating the valuable security report for any publicly accessible data in the S3 or the unencrypted buckets, including the ones shared with AWS Accounts outside the organization.

Below the summary, one can see the top findings by type and by S3 bucket. Overall, this page provides a great overview of the status of the S3 buckets.

Within the Findings section, we have the complete list of findings. One can select them to be archived, unarchived or just to export them for the reporting purposes. One can get full description and information about the findings collected by Macie.

The above-mentioned findings can also be viewed in the AWS web console and can be sent to Amazon CloudWatch Events for seamless incorporation with existing workflow or any 3rd party event management systems or to be infused with AWS Step Functions for automated remediation actions.
Within the S3 Buckets section, we can search and filter from the available buckets to create custom sensitive data discovery jobs across the selected or even multiple buckets to find sensitive data in objects, and to check encryption status and public accessibility at a very object level. Jobs can be executed once, or scheduled daily, weekly, or monthly.

For jobs, any changes in the given bucket or multiple selected are tracked automatically by Macie. It also evaluates any modifications or initiations in the objects over time. In the additional settings, one can include or exclude objects based on attributes like tags, size, file extensions, or last modified date. To monitor the costs and the use of the free trial, one can look at the Usage section of the console.

Conclusion
With all the astounding capabilities and benefits of Amazon GuardDuty and Amazon Macie, the learning coverage around these services lacks the gravitas it deserves. As the biggest cloud platform and provider, AWS has introduced several measures to automate and enhance the security pillar of the architectures built on it and making these services intelligent using machine learning is a leap ahead in the channel.



